Today, a new technology is reshaping the manufacturing landscape. Edge computing—a ubiquitous, distributed computing network—collects and processes data at the network’s outer boundary (“the edge”), closest to where users and endpoint devices intersect.
The addition of the Internet of Things (IoT) and other endpoint devices generates vast data sets, causing high latency, bandwidth congestion, and data bottlenecks in centralized networks. Analysts at Juniper Research predict that more than 46 billion IoT-connected devices will be in use by 2023, and the growth of robots, drones, and other complex devices will accelerate this shift.
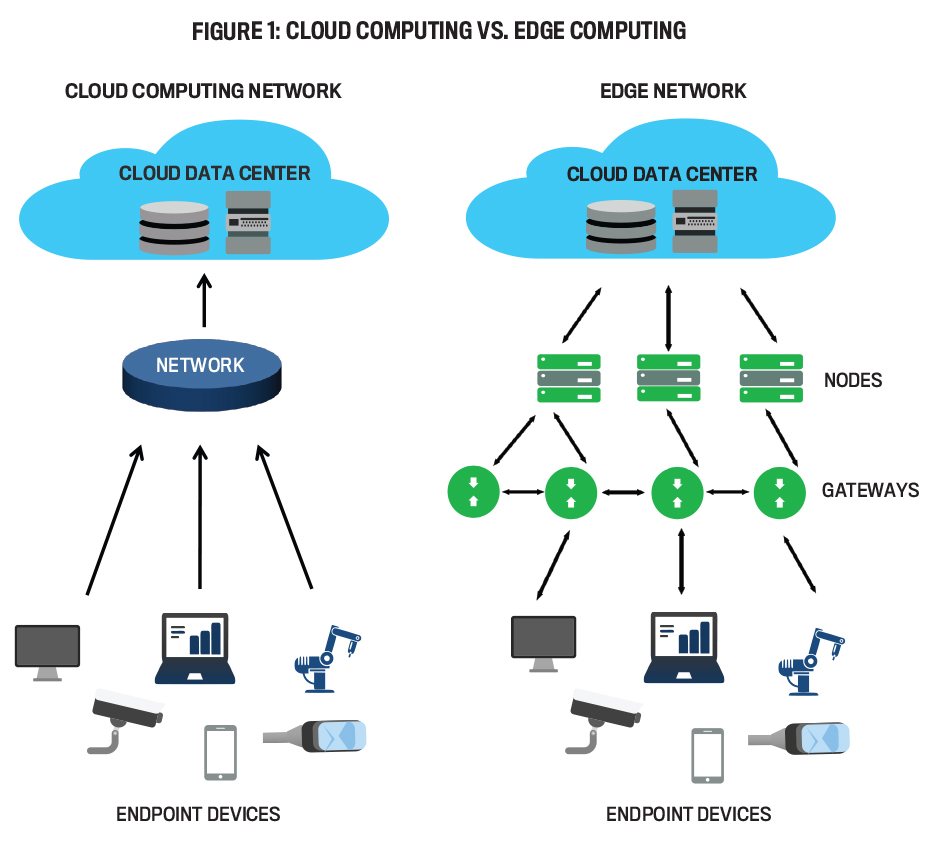
While a cloud architecture relies on centralized networks to analyze and process data, an edge network collects and sends data from endpoint devices (IoT, sensors, robots, autonomous vehicles, etc.) to intermediate gateways that analyze the data and perform computational tasks. Edge nodes then filter and transmit only relevant information to the cloud (see Figure 1).
What’s the upshot of these latest developments? For product manufacturers, moving more computing tasks to a network’s edge will increase speed and operational efficiency and provide a new agility to the factory floor.
EDGE COMPUTING ARCHITECTURE
Edge computing’s origins date back to the 1990s when content delivery networks (CDNs) placed nodes at closer proximities to end users. Edge computing enhanced CDN functionality by empowering nodes to perform computational tasks. (For more on this topic, see Mahadev Satyanarayanan, “The Emergence of Edge Computing,” Computer, January 2017.) An edge network isn’t a replacement for the cloud; instead, it’s an agile system that combines the benefit of cloud-based networks to create a hybrid model that enables connectivity between multiple endpoint devices.
Software giants such as Amazon, Microsoft, and Google are investing heavily in edge-based software to extend their cloud services and deliver distributed capabilities throughout the value chain. A study by Gartner estimates that almost 75% of data processing across diverse industries will occur at the network’s edge by 2025, up from about 10% currently (). Today, more companies are leveraging this collaborative technology as a preferred solution to improve connectivity and reduce network latency and bandwidth challenges.
Using an edge-based architecture has several advantages over centralized computing. First, many companies—yours may be one of them—maintain a mosaic of old and new systems that don’t interoperate well. Edge computing converts the communication protocols of legacy systems into a language that modern devices can understand, reducing the need to replace older industrial equipment and software.
Second, when network nodes transmit more data than a connection can support, bandwidth congestion occurs and causes throughput reduction or data loss. By processing more information at the network’s edge, only results are sent back to the cloud, thereby requiring fewer back-and-forth data transmissions. Third, there’s a growing interest in achieving ultralow latency targets (speeds of one millisecond or less).
Relocating more data-processing functions to endpoint devices increases data transfer capabilities—a critical success factor to aid in an organization’s decision making. Finally, if a cyberattack occurs, the dispersed infrastructure minimizes the amount of data at risk. The edge protocols can seal off compromised devices or nodes without shutting down an entire network.
CHANGING THE FACTORY FLOOR
Competitive pressures, combined with transformative changes in how companies make products, are reshaping the entire manufacturing value chain. The fourth industrial revolution, referred to as Industry 4.0 (see Figure 2), is the next generation of technologies and processes to reshape cyber-human interaction on the factory floor. The fusion of autonomous vehicles, IoT devices, and intelligent equipment is rapidly blurring the lines between physical and digital manufacturing. (See, for instance, Anton van der Merwe and Larry R. White, “AI for Decision Analysis,” Strategic Finance, February 2021.)
From conception to product delivery, companies that previously used a combination of manual and siloed systems now employ advanced robotics, AI, electronic wearables, and computer vision devices to design, manufacture, and test products. As the digitization of manufacturing increases, edge computing has a concomitant role in connecting, analyzing, and sharing data from endpoint devices and improving backroom functions, such as inventory management and predictive maintenance. For instance, smart shelving (sensors attached to inventory shelves or bins) can improve inventory management, and augmented reality smart glasses can assist with order picking and sorting; AI provides inventory updates for correct pricing and stocking levels; and automated pallets with sensors self-organize based on real-time demand.
Edge networks also provide bidirectional information—data sent and collected at the same time—to deliver uninterrupted inventory updates 50 times faster than a cloud environment and avoid overstocking, stock outages, and shrinkage, particularly during periods of peak demand or when extreme situations occur. (For more, see Raiyaan Serang, “Leading Edge: Beyond the Cloud,” KTech Bytes, June 6, 2019.)
For example, the COVID-19 pandemic heavily disrupted existing supply chains for products previously not subject to shortages. The slow reaction time—combined with consumers hoarding water, cleaning supplies, hand sanitizer, and other products—strained manufacturers on a global scale. By coalescing digital and physical processes with an edge network’s superior connectivity, companies can significantly improve the response time to shifting demands, stocking changes, and supply chain disruptions.
Unplanned equipment downtime affects both productivity and revenues. In the automotive industry, for example, downtime costs and productivity losses can range from $22,000 to $50,000 per minute. Many businesses still rely on a combination of manufacturer recommendations, physical inspections, and databases containing current and historical repair records to predict maintenance needs. Challenges occur when assets are in remote locations, manual examinations are too difficult (e.g., turbine blades, offshore oil platforms, etc.), or when usage exceeds standard guidelines.
A more holistic approach is to attach intelligent sensors to equipment, robots, and other assets to provide real-time information that detects loose, misaligned, or damaged parts before a failure occurs. For example, the French technology services corporation Capgemini utilizes a predictive asset maintenance solution combined with edge computing analytics to help companies expand their use of cloud and digital platforms.
The software monitors and analyzes data sent from each asset, recommends precise responses and actions, and uses modeling to predict machine failures and maintenance requirements. The edge architecture performs advanced analytics in real time and then transmits the information directly to managers and technicians (without causing bandwidth congestion) to the cloud. Continuous monitoring coupled with high-speed reporting optimizes operational performance and avoids costly disruptions.
Many companies, including the Coca-Cola Company, eBay, Cisco, and Intel, are investing in edge computing to solve problems or optimize their business operations. See “DAIHEN’s Data Journey” (at end of article) for a detailed example of how one company is using edge computing to modernize its manufacturing operations.
THE NEXT FRONTIER OF MANUFACTURING
Future smart factories will further transform how equipment, IoT devices, robots, and autonomous vehicles interact with each other. The fifth generation of mobile networking technology (5G) will further improve manufacturing operations by increasing connectivity on the factory floor. Speed is already a key benefit—5G is already 100 times faster than 4G, which improves data sharing and connectivity with multiple sensors and other devices simultaneously.
Currently, a single sensor can transmit an average of 43,200 signals in a 24-hour period. Factories with hundreds or thousands of sensors simultaneously sending data can overload cloud networks. In contrast, a robust 5G network will handle increased data transmission while maintaining low latency levels. Integrating 5G to the factory floor offers a highly connected, agile environment to enhance product assembly performance.
Advanced analytics software is another technology that can keep organizations highly competitive. It can aggregate multiple data sets and historical information simultaneously to gain efficiencies throughout the manufacturing value chain. In a smart factory context, advanced analytics focuses on qualitative improvements to optimize operations and reduce costs. For example, many companies face ongoing difficulties with defects, scrap, and rework problems, resulting in damaged customer satisfaction and possible product recalls.
Visual inspections and older software models are often insufficient to identify potential qualitative issues in a changing manufacturing environment. In contrast, advanced analytics-based intelligent software uses sophisticated algorithms and simulation programs to update data continuously and monitor evolving patterns to identify possible anomalies or quality issues.
Digital twinning—duplicating a physical asset to an evolving digital replica—is a recent innovation to Industry 4.0. A digital-twin design offers a new approach to gathering and communicating real-time information by pairing physical assets with a virtual environment. For example, engineers at Boeing can subject a digital twin of an airplane to real-world weather and flying conditions. Simulation tools and three-dimensional animation then provide predictive analytics and prevent manufacturing problems before they occur.
Previous efforts to utilize digital-twin designs were limited by bandwidth capacity, storage costs, and computing resources. Today, combining sensors and endpoint devices like IoT with an edge computing environment has removed these obstacles. According to Orbis Research, up to 85% of IoT platforms will contain some form of digital twinning by 2022. (For more information, see “Digital Twins-Global Market Outlook (2017-2026).”)
As you can see, advanced robotics will play a pivotal role in reimagining tomorrow’s production facilities. Many of today’s industrial robots operate with a wired system because older generations of wireless networks can’t support the speed needed to communicate programming instructions. The next generation of robots will have superior vision, faster mobility, improved adaptability, and more intelligence to act autonomously. For example, robots encoded with every detail of the manufacturing process and linked to AI-based programming could perform tasks and make real-time decisions without human direction. As prices for robots decline and their abilities increase, many industry analysts see a time when “lights out” manufacturing—where production activities are fully automated—is the new norm for the factory floor.
THE MANAGEMENT ACCOUNTANT’S ROLE
As a management accounting or finance professional, you have a crucial role in ensuring compliance with your organization’s record-keeping requirements, internal controls, and International Organization for Standardization (ISO) standards, among other responsibilities. In an era of intelligent automation where data is viewed as an essential business asset, cybersecurity is no longer reserved for the IT department because data security affects operations throughout the organization. (For more on facing down cyber threats, see Ramona Dzinkowski, “Cyber Risk: Time to Elevate the Agenda,” Strategic Finance, October 2019.)
Management accountants must also monitor new and existing controls to evaluate their effectiveness and report weaknesses that could affect the organization’s adherence to processes, policies, and applicable laws.
Sometimes, however, you have to look back before you can look ahead. Management accountants need both current and historical information for internal audits, supply chain monitoring, financial statements, and tax compliance. Record-keeping management is a critical accounting function and intersects with the IT department’s responsibility for designing systems that accurately collect and store data. A cloud environment gathers and sends all data from endpoint devices to a central server, providing a seamless monitoring process and continuous backup. Extracting data is relatively simple since a single repository arranges records in a meaningful way.
In contrast, the combination of bidirectional data flow, filtering only computational results to the central server, and the reliance on multiple systems to create backup files in an edge environment can limit data visibility and possibly compromise decision-making efforts. While relocating computational processing to endpoint devices has several benefits, including lower latency and improved operational efficiency, new controls are necessary for the custody and control of records from the point of origin to archival storage. Your role should therefore include coordinating with the IT department to establish storage and backup processes for all nodes and servers and to create passwords and tracking mechanisms for endpoint devices to prevent data loss or theft.
Another area of concern is the use of internal controls to safeguard confidential information, prevent fraudulent entries, and maintain the reliability and accuracy of manufacturing data. The edge computing environment is a highly decentralized architecture, using endpoint devices to increase machine-to-machine information flow and reduce manual evaluation. Even though edge computing adds speed and agility to the factory floor, accounting oversight is necessary to monitor inventory controls, procurement, and other functions that may be affected by system changes. For example, a failure by an endpoint device to communicate low inventory levels to a server could result in a production line work stoppage.
WHAT DOES THE ISO SAY?
When new system implementations affect multiple departments and change how data is received and transmitted, management accountants and other financial professionals are responsible for performing internal control risk assessments and reporting their findings to senior management.
ISO also views manufacturing through a lens of integrated processes and a framework consisting of customized instructions, procedures, and standards. ISO’s governing body employs technical committees to develop new standards, using a consensus approach to analyze feedback from stakeholders worldwide. Accounting, operations, IT, and other departments are responsible for performing periodic audits to monitor and evaluate compliance with customer and regulatory requirements. As more companies expand operations internationally across borders, manufacturers are continuously updating their certifications and integrating them throughout the entire organization.
For example, manufacturing companies are combining the international ISO 27001 framework shown in Figure 3 with other established certifications like ISO 9001:14000. While these standards focus on defining processes, controls, and documentation, ISO 27001 is a comprehensive information security management system (ISMS) designed to protect information consistent with increasingly rigid regulatory requirements, such as the European Union’s General Data Protection Regulation, the National Institute of Standards and Technology’s Cybersecurity Framework, and the Sarbanes-Oxley Act of 2002. The ISMS is a set of standards that manage risks such as cyberattacks, data leaks, or theft, and analyzes interfaces and dependencies between departments and processes.
In short, combining factory-floor automation with evolving ISO standards requires management accountants to have a coordinating role with IT and senior management to implement and oversee compliance with company-wide data security guidelines.
BENEFITS, BUT CHALLENGES TOO
As a nascent technology, edge computing offers both benefits and barriers to successful implementation. The main advantage of using a centralized network is achieving economies of scale. Shared resources—including systems, data storage, programming, cybersecurity, and software changes—are centrally controlled.
Small businesses departing from less expensive, established system architectures will require a substantial investment coupled with increased maintenance and IT support. Building an edge infrastructure is costly, involves significant planning and logistical preparations, and requires considerable software and hardware resources. For example, adding more endpoint devices or a new inventory storage area requires more servers and peripheral devices. In contrast, a centralized server utilizes the same infrastructure regardless of changes or additions to the factory layout.
The addition of endpoint devices, servers, and other peripheries also increases the overhead expenses necessary to maintain them. For small businesses without remote locations or those producing low-complexity items, an edge network may yield some efficiency gains but may not be cost-effective to implement.
Protecting numerous endpoint devices and nodes containing sensitive data from theft or loss presents a considerable challenge for edge networks. Unlike security procedures in a centralized network—which enables seamless software updates, multiple data backups, and firewall upgrades—a highly decentralized system has numerous points of vulnerability. While edge architectures can reduce attacks on centralized servers, endpoint devices such as laptops, mobile devices, and smart glasses can break or be lost or stolen.
Attack vectors—the paths used by hackers to gain unlawful access to networks—may easily penetrate endpoint devices or nodes because they have limited encryption or firewall protections. As more companies install edge networks, the addition of devices capable of performing increasingly complex functions further away from centralized servers will also increase. Addressing security risks, achieving economies of scale, and protecting sensitive data from hackers are some of the barriers remaining before edge computing gains widespread acceptance.
The creation of the assembly line had a transformative effect on manufacturing speed, efficiency, and quality. As manufacturing migrates toward a sophisticated, cyber-human ecosystem where machines and employees work side by side, the confluence of 5G, Industry 4.0, and edge computing will provide greater agility, flexibility, and intelligence to support these changes.
While barriers such as high investment costs and cybersecurity concerns currently limit widespread adoption, edge computing is creating new opportunities to modernize factories and digitize manufacturing processes. With new industrial revolutions on the horizon, ushering in more automation and connectivity, someday all companies may be computing on the edge.
DAIHEN’S DATA JOURNEY
THE COMPANY
DAIHEN Corporation was founded in 1919 as the Osaka Transformer Co., Ltd. In 1985, the company changed its name to DAIHEN. A global industrial electronics leader with numerous business segments and operations worldwide, DAIHEN manufactures, sells, and repairs various transformers, welding machines, and industrial robots. The company also manufactures energy and semiconductor-related equipment, such as electric power transmission products, dispersed power systems, and various types of control communication equipment.
THE CHALLENGE
DAIHEN wanted to digitize operations at its plant in Osaka, Japan. Each electric transformer required more than 200 inspections, which consumed almost 30% of production time. The regulatory climate, coupled with stringent quality standards, required tracking large amounts of performance data. Manually entering high volumes of data made cloud computing cost-prohibitive, and traditional methods of offline data analysis were insufficient to meet the requirements. In response, DAIHEN partnered with FogHorn, a developer of edge AI software, to find a more efficient way to reduce manual inspections, improve overall assembly visibility, and provide real-time production analytics.
THE SOLUTION
To automate data tracking, FogHorn built a radio-frequency identification (RFID) system and a sensor infrastructure to monitor productivity and to track the location of parts. Condition-monitoring sensors collected environmental measurements, including humidity, dust, and temperature, in the clean rooms. FogHorn software then processed and provided real-time analytics to identify production issues and improve efficiency. The new RFID and sensor system enabled real-time visibility to each detail of the product life cycle while eliminating the need for workers to provide production updates manually.
THE RESULTS
Within six months, the new RFID and sensor system enabled DAIHEN to see how parts were stored, built, and assembled, with granular detail of each manufacturing stage. The company saved almost 1,800 hours per year, provided real-time analytics for management, and improved benchmark yields. The efficiency improvements eliminated the need to manually inspect the transformers. The next phase increased factory coverage from 70% to 100% and the time savings to 5,000 hours per year. As a result, DAIHEN has deployed the system in several of its other factories throughout Japan.

April 2021